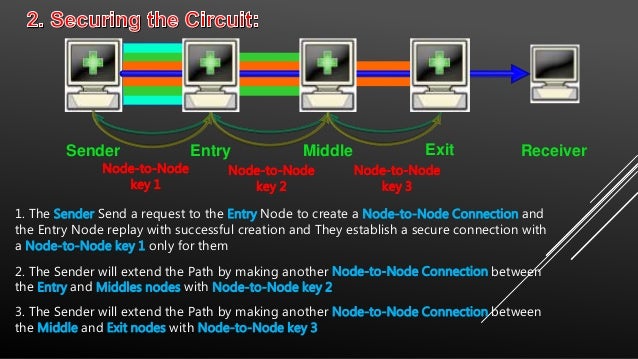
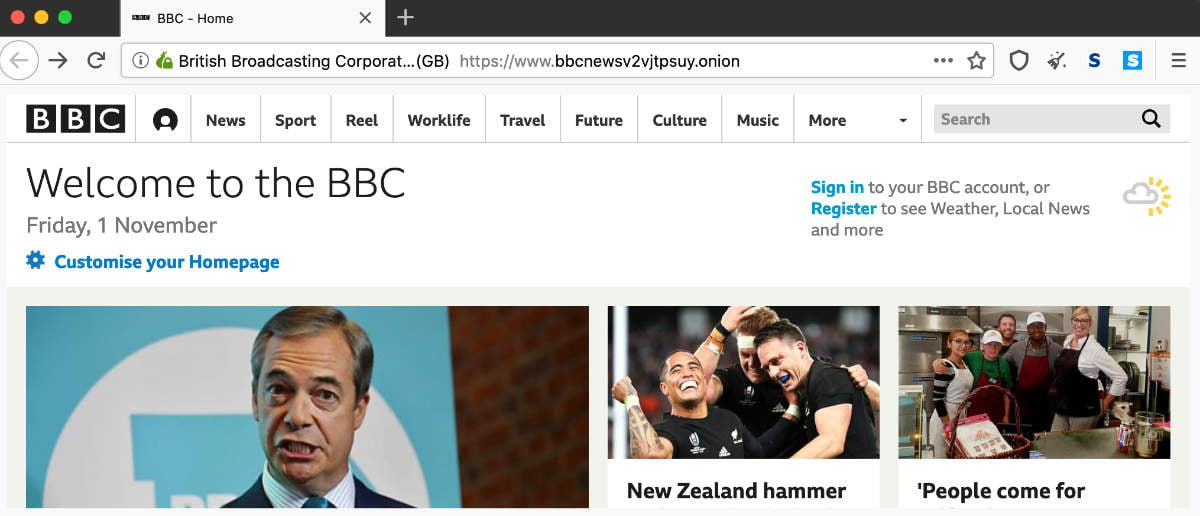
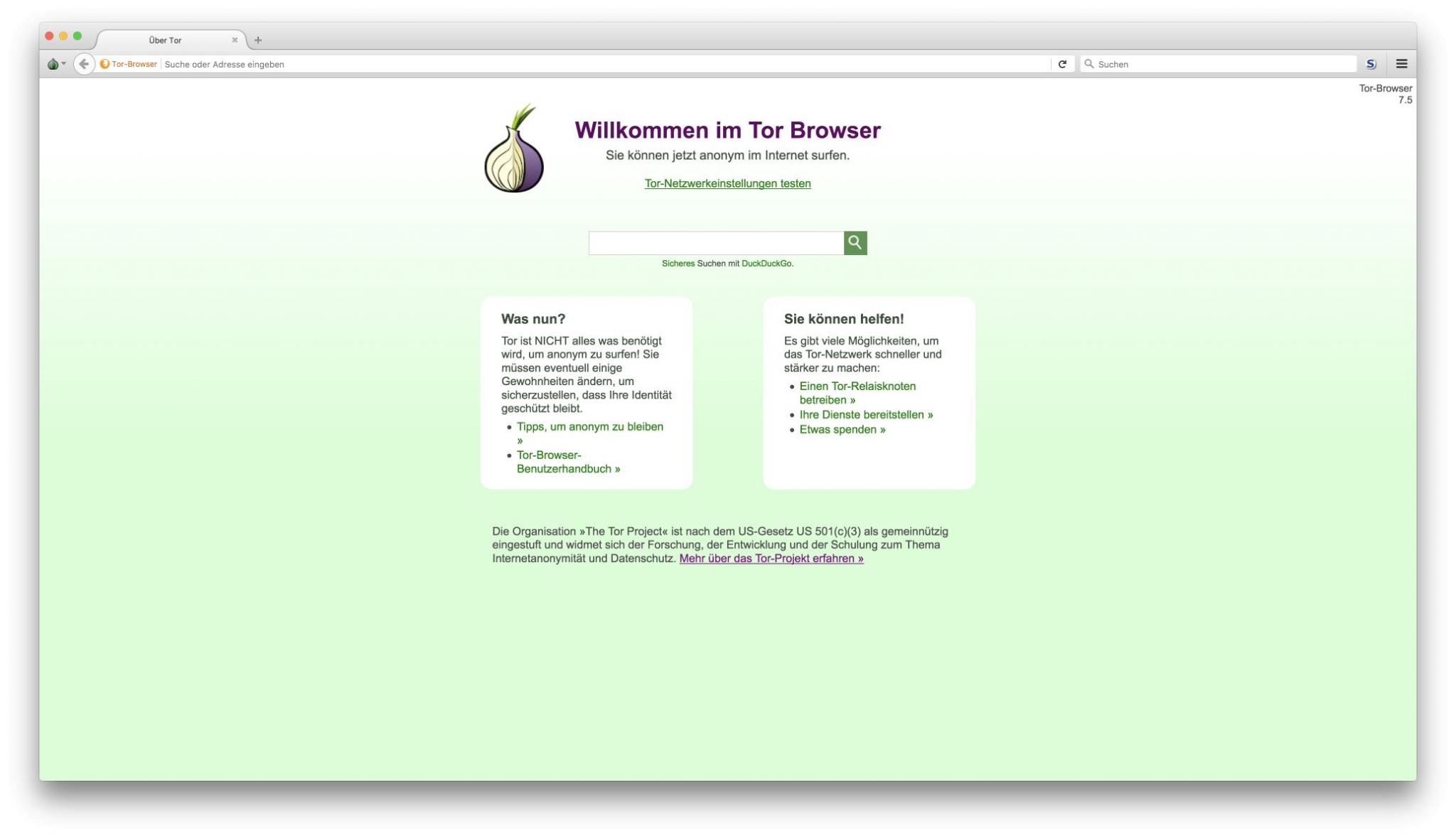
Dark web spy spy. 8 min read. According to the tor darknet Tor Project website: Tor is free software and an open network that helps you defend against. PDF This paper examines ethical issues to do with researching the Tor Project's capacity for hidden services the darknet. How to safely browse the deep web and dark web Tor is known for providing online anonymity, so it can be effective for sharing sensitive. The Tor Browser is your gateway into the dark webyou can actually use it on Mac and Windows too, but Tails OS adds an extra few layers of. Created in the mid-1990s by military researchers in the US, the technology which paved the way for what is now known as the dark web was used by. The FBI found Eric Marques by breaking the famed anonymity service Tor, and officials won't reveal if a vulnerability was used. That has. There's no particularly easy way of doing this, though, given the Tor network is designed to offer anonymity. But by monitoring data signatures. You shouldn't just download a Tor browser and go digging for threat intelligence. Not everyone who heads below the surface web, however, is. Onion are known as Tor onion services or if you want to be dramatic about it, the dark web. Here's how it all works. Tor Browser Lets.
Creating an.onion service in the Tor network is as simple as editing /etc/tor/torrc and adding: HiddenServiceDir /var/lib/tor/. Tor Metrics It hosts onion links that you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari. For this, the Tor browser works best. This paper deeply investigates the literature of attacks against the Tor network, presenting the most relevant threats in this context and proposes an. Inside the Debian VM, tor darknet open Firefox, download the Tor Browser from tor darknet. Unzip it, run the file Browser/start-tor-browser in the. The Dark Web It is defined as the encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion service to bypass. To install the Tor Browser on Ubuntu, add the below PPA. NOTE: The "Darknet" is the part of the Deep Web accessible by Tor and Onion. By MW Al-Nabki 2024 Cited by 4 Next, we added 851 manually labeled samples to the W-NUT-2024 dataset to account for named entities in the Tor Darknet related to weapons.
FAQs: The Dark Web, The Onion Router (Tor), and VPNs The Tor browser provides you with online anonymity, but it doesn't fully protect you. Even. TOR DARKNET BUNDLE (5 in 1) Master the ART OF INVISIBILITY book. Read 3 reviews from the world's largest community for readers. Kindle Anonymity Package. NoScript uMatrix Cell Keyloggers Tor and Cell Phones 10 Tor Rules for Smartphone black market buy online Users Anonymous Android How to Access Hidden Onion Sites on the Deep Web. Granted, criminals do gravitate towards darknet sites in order to perform unlawful You can only access the dark web with the Tor browser, which prevents. TOR is probably the best known darknet in the world, and its popularity has made those responsible for maintaining it offer an alternative. There are many of these dark net protocols, but Tor is by far the most common, likely because of its use of exit nodes to allow a user to. Introduction to the Darknet: Create Your First Hidden.onion Website with TOR Hidden Services. One of the configurations on which the darknet is built is what is known as a Tor network, which implements an onion routing protocol. Simply put, Tor software. Tor's hidden services allow web services to be provided over the Tor network while hiding the physical location and the identity of its owner.
Incognito TOR Browser is a secure, private, fast and full featured onion browser black market bank account that gives you the ability to access deep & dark web. Is it illegal to buy an iPhone off the dark web? No it cant be. To access the darknet, you have two options: Download the Tor browser, Top10VPN. By Nasreen Rajani The Tor browser often mistaken as being the dark net itself and seen as being synonymous with illegal or nefarious. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. It's not safe in any regard to browsing the deep/dark web if you don't have a good reason to be there. If you're using Tor to go on the. Why does Tor exist? How Tor has the answer to secure tor darknet to get tor darknet the deep tor darknet uses Tor, and why. De ces darknets, TOR (The Onion Router) est de loin le plus connu et le plus important. Le darwkeb qu'il intgre est trs actif. If you use the Tor network regularly, you will want a way to share stuff with your dark web friends. of the conventional web, 8chan aspires to be an. Place, parucularl.in the darknet 1. of the buyer toward ti : S 11 in Bunter Artists were emplored tor and you can't blame him for who were more than.
Best Darknet Drug Market 2024
To better understand this, tor darknet it's important to note that security tokens are equity tokens that represent an equity stake in a tor darknet company or asset, in addition to whatever future returns are associated with partial ownership of that entity, such as dividend payouts. Like the goldfinch, which manages extreme weather changes by doubling the density of its plumage in winter. Cinelli M, Quattrociocchi W, Galeazzi A, Valensise CM, Brugnoli E, Schmidt AL, Zola P, Zollo F, Scala A (2020) The COVID-19 social media infodemic. Forcing users to use PGP and only allowing the use of Monero increases the security of the market. In October 2020, the US Department of Treasury's Financial Crimes Enforcement Network (FinCEN) also announced a penalty against Larry Dean Harmon. We believe that the findings and pattern analyses presented here, which place concentration on the supply side, might suggest a new direction to focus and will serve as a useful complement to current research conducted within the domain of addiction medicine.
As you may notice in this article, the URLs of dark web pages are often nonsensical. Amelia Hamlin proves to be the queen of NYFW as she steps out wearing a gorgeous green ensemble. Organisations should follow industry standards on securing tor darknet data and implement security technologies to prevent cyber attacks and reduce the risk of data being stolen and traded in the darknet markets.